Protecting SAP
Preventively protect sensitive assets for the organization contained in ERP systems
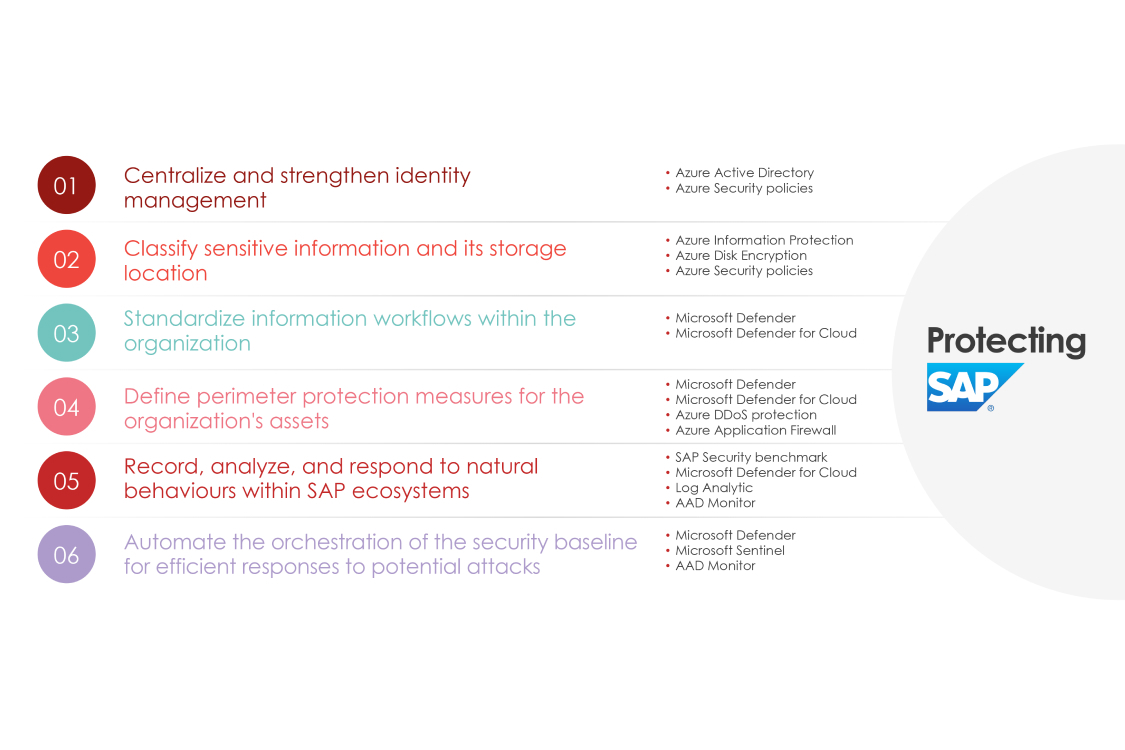
Using Azure Security components and our specialized services, it is possible to control and mitigate data leaks events for SAP customers looking to offer highly reliable environments.
Value Proposition
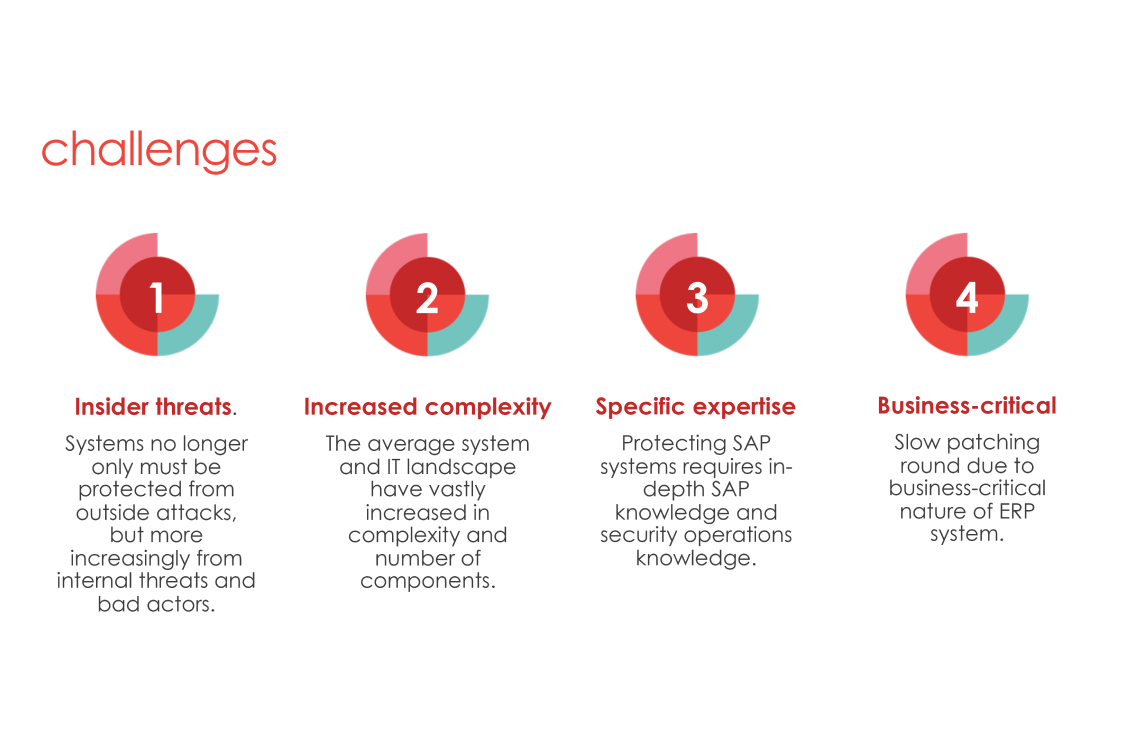
Having your confidential workloads in the cloud, it is normal to deal with these situations such as:
- The complexity of SAP platform security?
- A possible migration or current use of sensitive information in the Cloud?
The world is constantly digitizing. The decentralization of sensitive information and migration to the cloud is a reality for so many organizations, so the growing record of events and incidents of data leaks results in the constant global need to mitigate threats and improve cybersecurity in SAP systems.
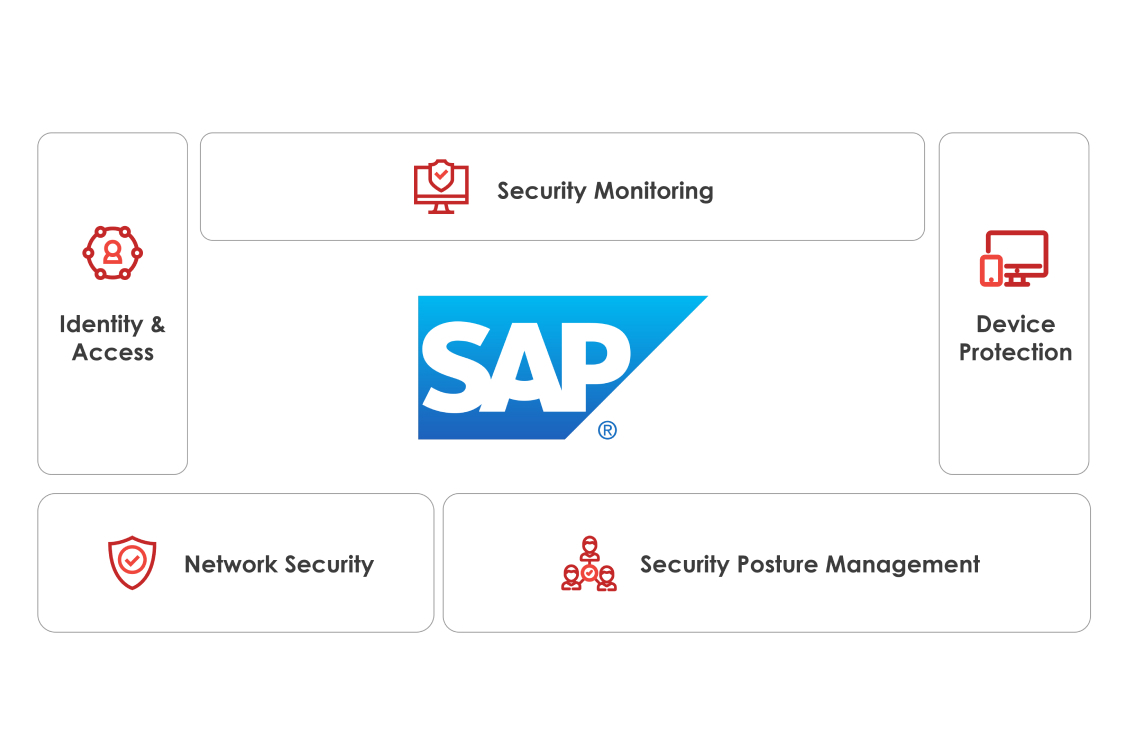
Our solution reinforces the correct use and control of sensitive assets for the business in a continuous and automated way through defined processes for efficient data management, authentication, and access to resources in SAP and the cloud, supporting and using Microsoft Azure security features and best practices.
Features
- Ensure secure access to your systems data and assets. Understanding that data in ERP systems must be protected from the inside as if it were outside the Internet.
- Record, review and inspect events trying to identify abnormal behavior in the different SAP and Azure services.
- Ensure visibility, accurate analysis, orchestration, and automation to keep up with cyberattacks.
Pricing Plan
Ad-hoc Protecting SAP with Azure
Managed delaware security services
Package consulting services
- Complete security baseline design for your SAP systems (Full findings document+implementation+best practices)
- Basic settings for identity and data management, labeling, DLP and basic scheme for advanced information protection settings based in Microsoft Defender and Sentinel
- Comprehensive scanning and detection based on real reports of components and services
Protecting SAP: 3 day workshop
Protecting SAP (on-premise or hosted on Azure)
The workshops are planned on a period of 4 weeks.
- Protecting SAP systems (on-premise or hosted on Azure) using the power of Microsoft Cloud based security. Protecting SAP systems is challenging.
- During the workshops our experts will asses the current level of protection of your SAP ERP system, identify weaknesses in your ERP landscape and create a plan increase the level of protection on short term and on the long term.
Workshops
Day 1: Getting to know the landscape, challenges of today and vision towards the future.
Day 2: In-depth sessions
Day 3: Presenting strengths and weaknesses together with a short term actionable plan and a long term guidance